windbg使用教程,attach 的左下角非入侵式就是不能下断点。
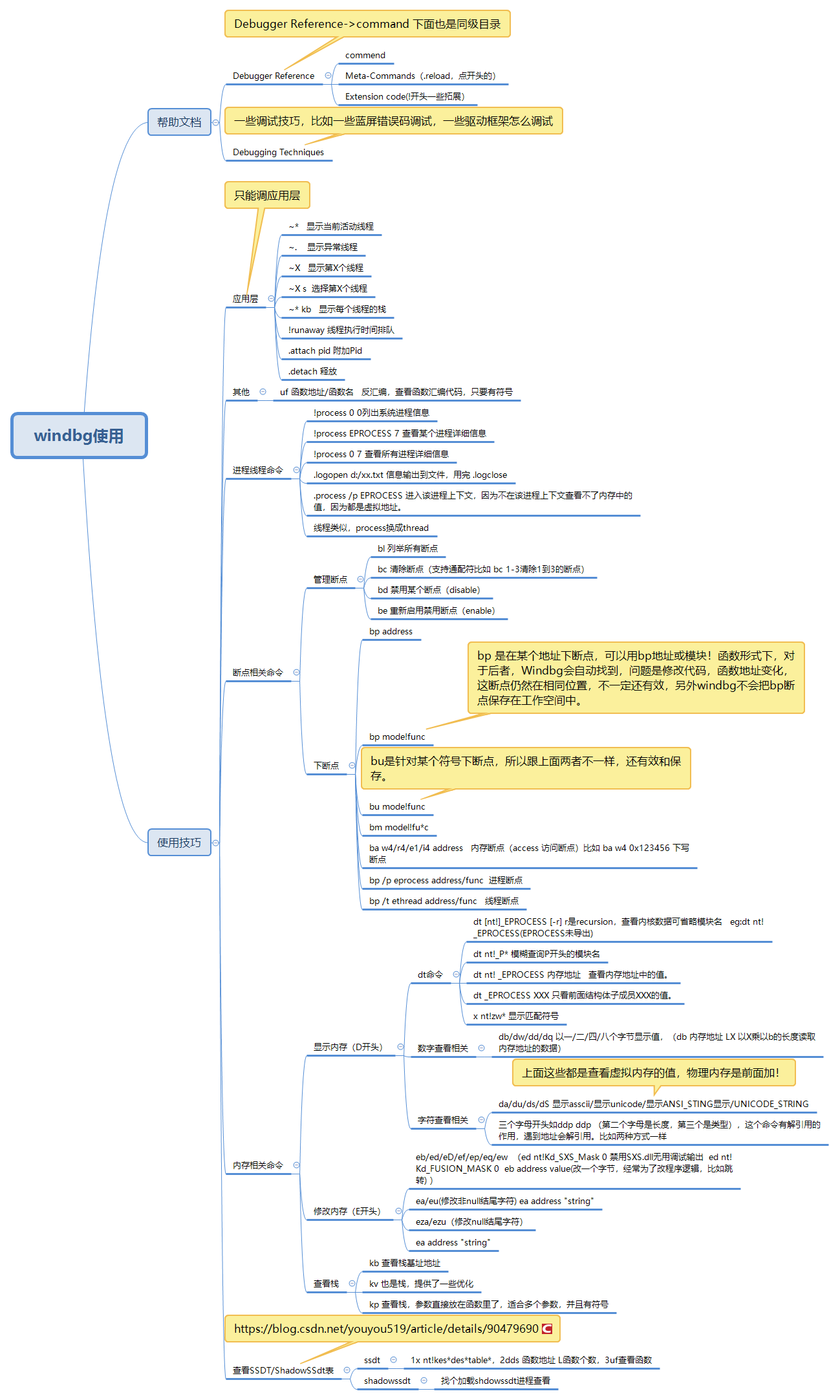
应用层常用命令
~* 显示当前活动进程
~. 显示异常线程
~X 显示第X个线程
~X s 选择第X个线程
~* kb 显示每个线程的栈
!runaway 线程执行时间排队
.attach pid 附加Pid
.detach 释放
断点
管理断点命令(支持通配符比如 bc 1-3清除1到3的断点)
bl 列举所有断点
bc 清除断点
bd 禁用某个断点(disable)
be 重新启用禁用断点(enable)
下断点命令
bp address
bp mode!func
bu mode!func
bm model!fu*c
ba w4/r4/e1/i4 address 内存断点(access 访问断点)比如 ba w4 0x123456 下写断点
bp /p eprocess address/func 进程断点
bp /t ethread address/func 线程断点
bp 是在某个地址下断点,可以用bp地址或模块!函数形式下,对于后者,Windbg会自动找到,问题是修改代码,函数地址变化,这断点仍然在相同位置,不一定还有效,另外windbg不会把bp断点保存在工作空间中。
bu是针对某个符号下断点,所以跟上面两者不一样,还有效和保存。
此外模块未加载,函数地址不存在,bp会失败,bu不会。新版windbg的bp失败会转bu。
显示内存
D系列内存查看命令(display tag 显示类型)
dt命令
查看某些结构体的值,
dt [nt!]_EPROCESS [-r] eg:dt nt!_EPROCESS(EPROCESS未导出)
EPROCESS
EPROCESS介绍
中间有一些重要字段DebugPort(反调试反反调试),Token(进程的一些权限),ImageFileName(存放进程名字)
想查看结构体里面的结构
dt _EPROCESS -r 递归展开子结构体(r是recursion,查看内核数据可省略模块名)
dt nt!_P* 模糊查询P开头的模块名
dt nt! _EPROCESS 内存地址 查看内存地址中的值。
dt _EPROCESS PEB 只看前面结构体子成员的值。
x nt!zw* 显示匹配符号
数字查看相关
db 以一个字节显示值,(db 内存地址 LX 以X乘以b的长度读取内存地址的数据)
dw 以两个字节查看内存的值 (db 内存地址 LX 以X乘以w的长度读取内存地址的数据)
dd 以四个字节长度查看内存的值
dq 8个字节
字符查看相关
da 显示asscii
du 显示unicode
ds 显示ANSI_STING
dS 显示UNICODE_STRING
上面这些都是查看虚拟内存的值,物理内存是前面加!
三个字母开头的命令
ddp (第二个字母是长度,第三个是类型),这个命令有解引用的作用,遇到地址会解引用。比如两种方式一样
1
kd> ddu 0x87679718+0x01c+0x004 L1
87679738 85efe488 "Driverntmodeldrv.藯.Љ慖.蕀蝘.虴瑐蝖র"
2
kd> dd 0x87679718+0x01c+0x004 L1
87679738 85efe488
kd> du 85efe488
85efe488 "Driverntmodeldrv.藯.Љ慖.蕀蝘.虴瑐蝖র"
修改内存
eb/ed/eD/ef/ep/eq/ew
ea/eu(修改非null结尾字符)
eza/ezu(修改null结尾字符)
ea address "string"
ed nt!Kd_SXS_Mask 0 禁用SXS.dll无用调试输出
ed nt!Kd_FUSION_MASK 0
eb address value(改一个字节,经常为了改程序逻辑,比如跳转)
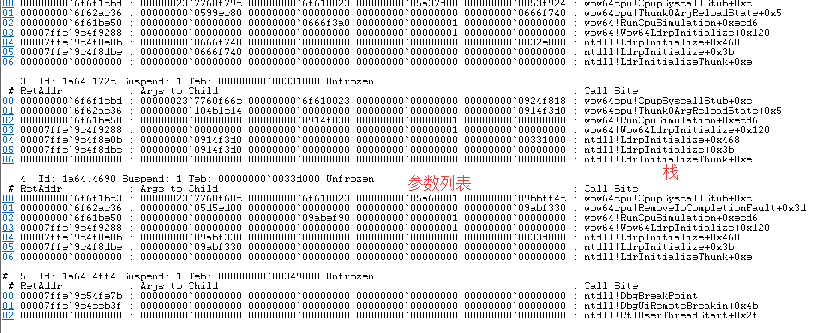
栈查看命令
kb 查看栈基址地址
kd> kb
ChildEBP RetAddr Args to Child
96063b44 83e41593 8792dd98 877da210 877da210 ntmodeldrv!DispatchRead+0x6 [d:mallocfree_2018windows1firstl-hellodemo2drivermodelntmodelntdrv.c @ 43]
96063b5c 8403599f 877da210 877da280 8741f560 nt!IofCallDriver+0x63
96063b7c 8406e2da 8792dd98 8741f560 00000001 nt!IopSynchronousServiceTail+0x1f8
96063c08 83e481ea 8792dd98 877da210 00000000 nt!NtReadFile+0x644
96063c08 76fb70b4 8792dd98 877da210 00000000 nt!KiFastCallEntry+0x12a
0012e060 76fb62c4 7525e072 0000004c 00000000 ntdll!KiFastSystemCallRet
0012e064 7525e072 0000004c 00000000 00000000 ntdll!NtReadFile+0xc
0012e0c8 76d2974f 0000004c 0012fa40 00000400 KERNELBASE!ReadFile+0x118
0012e110 0042df35 0000004c 0012fa40 00000400 kernel32!ReadFileImplementation+0xf0
//96063b44 83e41593 8792dd98 这三个分别就是ebp返回地址,第一个参数
比如这个函数第一个参数是DEVICE_OBJECT
kd> dt _DEVICE_OBJECT 8792dd98
csrss!_DEVICE_OBJECT
+0x000 Type : 0n3
+0x002 Size : 0xb8
+0x004 ReferenceCount : 0n1
+0x008 DriverObject : 0x87679718 _DRIVER_OBJECT
+0x00c NextDevice : (null)
+0x010 AttachedDevice : (null)
+0x014 CurrentIrp : (null)
+0x018 Timer : (null)
+0x01c Flags : 0x44
+0x020 Characteristics : 0
+0x024 Vpb : (null)
+0x028 DeviceExtension : (null)
+0x02c DeviceType : 0x22
+0x030 StackSize : 1 ''
+0x034 Queue : <unnamed-tag>
+0x05c AlignmentRequirement : 0
+0x060 DeviceQueue : _KDEVICE_QUEUE
+0x074 Dpc : _KDPC
+0x094 ActiveThreadCount : 0
+0x098 SecurityDescriptor : 0x8aa5ac18 Void
+0x09c DeviceLock : _KEVENT
+0x0ac SectorSize : 0
+0x0ae Spare1 : 0
+0x0b0 DeviceObjectExtension : 0x8792de50 _DEVOBJ_EXTENSION
+0x0b4 Reserved : (null)
kv 也是栈,提供了一些优化
kp 查看栈,参数直接放在函数里了,适合多个参数,并且有符号
kd> kp
ChildEBP RetAddr
96063b44 83e41593 ntmodeldrv!DispatchRead(struct _DEVICE_OBJECT * pObject = 0x8792dd98, struct _IRP * pIrp = 0x877da210)+0x6 [d:mallocfree_2018windows1firstl-hellodemo2drivermodelntmodelntdrv.c @ 43]
96063b5c 8403599f nt!IofCallDriver+0x63
96063b7c 8406e2da nt!IopSynchronousServiceTail+0x1f8
96063c08 83e481ea nt!NtReadFile+0x644
96063c08 76fb70b4 nt!KiFastCallEntry+0x12a
0012e060 76fb62c4 ntdll!KiFastSystemCallRet
0012e064 7525e072 ntdll!NtReadFile+0xc
0012e0c8 76d2974f KERNELBASE!ReadFile+0x118
0012e110 0042df35 kernel32!ReadFileImplementation+0xf0
WARNING: Frame IP not in any known module. Following frames may be wrong.
0012fe54 0042e371 0x42df35
0012ff88 76d33c45 0x42e371
0012ff94 76fd37f5 kernel32!BaseThreadInitThunk+0xe
0012ffd4 76fd37c8 ntdll!__RtlUserThreadStart+0x70
0012ffec 00000000 ntdll!_RtlUserThreadStart+0x1b
进程线程命令
!process 0 0列出系统进程信息
!process EPROCESS 7 查看某个进程详细信息
!process 0 7 查看所有进程详细信息
.logopen d:/xx.txt 信息输出到文件,用完 .logclose
.process /p EPROCESS 进入该进程上下文,因为不在该进程上下文查看不了内存中的值,因为都是虚拟地址。
kd> dt _EPROCESS 876589b0
ntdll!_EPROCESS
+0x000 Pcb : _KPROCESS
+0x098 ProcessLock : _EX_PUSH_LOCK
+0x0a0 CreateTime : _LARGE_INTEGER 0x1d5108b`d0d0aa48
+0x0a8 ExitTime : _LARGE_INTEGER 0x0
+0x0b0 RundownProtect : _EX_RUNDOWN_REF
+0x0b4 UniqueProcessId : 0x0000056c Void
+0x0b8 ActiveProcessLinks : _LIST_ENTRY [ 0x8766bb08 - 0x87649cf8 ]
+0x0c0 ProcessQuotaUsage : [2] 0x664c
+0x0c8 ProcessQuotaPeak : [2] 0x7a5c
+0x0d0 CommitCharge : 0x1db3
+0x0d4 QuotaBlock : 0x874cc580 _EPROCESS_QUOTA_BLOCK
+0x0d8 CpuQuotaBlock : (null)
+0x0dc PeakVirtualSize : 0x104e5000
+0x0e0 VirtualSize : 0xe5de000
+0x0e4 SessionProcessLinks : _LIST_ENTRY [ 0x875f5114 - 0x87649d24 ]
+0x0ec DebugPort : (null)
+0x0f0 ExceptionPortData : 0x873f3828 Void
+0x0f0 ExceptionPortValue : 0x873f3828
+0x0f0 ExceptionPortState : 0y000
+0x0f4 ObjectTable : 0x8c838650 _HANDLE_TABLE
+0x0f8 Token : _EX_FAST_REF
+0x0fc WorkingSetPage : 0x1e387
+0x100 AddressCreationLock : _EX_PUSH_LOCK
+0x104 RotateInProgress : (null)
+0x108 ForkInProgress : (null)
+0x10c HardwareTrigger : 0
+0x110 PhysicalVadRoot : (null)
+0x114 CloneRoot : (null)
+0x118 NumberOfPrivatePages : 0xfd7
+0x11c NumberOfLockedPages : 0
+0x120 Win32Process : 0xfe962380 Void
+0x124 Job : (null)
+0x128 SectionObject : 0x8c838590 Void
+0x12c SectionBaseAddress : 0x00030000 Void
+0x130 Cookie : 0x417f32c2
+0x134 Spare8 : 0
+0x138 WorkingSetWatch : (null)
+0x13c Win32WindowStation : 0x00000030 Void
+0x140 InheritedFromUniqueProcessId : 0x0000054c Void
+0x144 LdtInformation : (null)
+0x148 VdmObjects : (null)
+0x14c ConsoleHostProcess : 0
+0x150 DeviceMap : 0x8e9d8a38 Void
+0x154 EtwDataSource : 0x877464c0 Void
+0x158 FreeTebHint : 0x7ffdd000 Void
+0x160 PageDirectoryPte : _HARDWARE_PTE_X86
+0x160 Filler : 0
+0x168 Session : 0x8ef75000 Void
+0x16c ImageFileName : [15] "explorer.exe"
+0x17b PriorityClass : 0x2 ''
+0x17c JobLinks : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x184 LockedPagesList : (null)
+0x188 ThreadListHead : _LIST_ENTRY [ 0x876588e8 - 0x8748b630 ]
+0x190 SecurityPort : (null)
+0x194 PaeTop : 0x867cc2c0 Void
+0x198 ActiveThreads : 0x1a
+0x19c ImagePathHash : 0x7a3328da
+0x1a0 DefaultHardErrorProcessing : 0
+0x1a4 LastThreadExitStatus : 0n0
+0x1a8 Peb : 0x7ffdb000 _PEB
+0x1ac PrefetchTrace : _EX_FAST_REF
+0x1b0 ReadOperationCount : _LARGE_INTEGER 0x745
+0x1b8 WriteOperationCount : _LARGE_INTEGER 0xb
+0x1c0 OtherOperationCount : _LARGE_INTEGER 0x24ce
+0x1c8 ReadTransferCount : _LARGE_INTEGER 0x1dc751
+0x1d0 WriteTransferCount : _LARGE_INTEGER 0x2a4
+0x1d8 OtherTransferCount : _LARGE_INTEGER 0x46d39
+0x1e0 CommitChargeLimit : 0
+0x1e4 CommitChargePeak : 0x2235
+0x1e8 AweInfo : (null)
+0x1ec SeAuditProcessCreationInfo : _SE_AUDIT_PROCESS_CREATION_INFO
+0x1f0 Vm : _MMSUPPORT
+0x25c MmProcessLinks : _LIST_ENTRY [ 0x8766bcac - 0x87649e9c ]
+0x264 HighestUserAddress : 0x7fff0000 Void
+0x268 ModifiedPageCount : 0x5d
+0x26c Flags2 : 0xd000
+0x26c JobNotReallyActive : 0y0
+0x26c AccountingFolded : 0y0
+0x26c NewProcessReported : 0y0
+0x26c ExitProcessReported : 0y0
+0x26c ReportCommitChanges : 0y0
+0x26c LastReportMemory : 0y0
+0x26c ReportPhysicalPageChanges : 0y0
+0x26c HandleTableRundown : 0y0
+0x26c NeedsHandleRundown : 0y0
+0x26c RefTraceEnabled : 0y0
+0x26c NumaAware : 0y0
+0x26c ProtectedProcess : 0y0
+0x26c DefaultPagePriority : 0y101
+0x26c PrimaryTokenFrozen : 0y1
+0x26c ProcessVerifierTarget : 0y0
+0x26c StackRandomizationDisabled : 0y0
+0x26c AffinityPermanent : 0y0
+0x26c AffinityUpdateEnable : 0y0
+0x26c PropagateNode : 0y0
+0x26c ExplicitAffinity : 0y0
+0x270 Flags : 0x144d0801
+0x270 CreateReported : 0y1
+0x270 NoDebugInherit : 0y0
+0x270 ProcessExiting : 0y0
+0x270 ProcessDelete : 0y0
+0x270 Wow64SplitPages : 0y0
+0x270 VmDeleted : 0y0
+0x270 OutswapEnabled : 0y0
+0x270 Outswapped : 0y0
+0x270 ForkFailed : 0y0
+0x270 Wow64VaSpace4Gb : 0y0
+0x270 AddressSpaceInitialized : 0y10
+0x270 SetTimerResolution : 0y0
+0x270 BreakOnTermination : 0y0
+0x270 DeprioritizeViews : 0y0
+0x270 WriteWatch : 0y0
+0x270 ProcessInSession : 0y1
+0x270 OverrideAddressSpace : 0y0
+0x270 HasAddressSpace : 0y1
+0x270 LaunchPrefetched : 0y1
+0x270 InjectInpageErrors : 0y0
+0x270 VmTopDown : 0y0
+0x270 ImageNotifyDone : 0y1
+0x270 PdeUpdateNeeded : 0y0
+0x270 VdmAllowed : 0y0
+0x270 CrossSessionCreate : 0y0
+0x270 ProcessInserted : 0y1
+0x270 DefaultIoPriority : 0y010
+0x270 ProcessSelfDelete : 0y0
+0x270 SetTimerResolutionLink : 0y0
+0x274 ExitStatus : 0n259
+0x278 VadRoot : _MM_AVL_TABLE
+0x298 AlpcContext : _ALPC_PROCESS_CONTEXT
+0x2a8 TimerResolutionLink : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x2b0 RequestedTimerResolution : 0
+0x2b4 ActiveThreadsHighWatermark : 0x28
+0x2b8 SmallestTimerResolution : 0
+0x2bc TimerResolutionStackRecord : (null)
kd> dt _PEB 0x7ffdb000
csrss!_PEB
+0x000 InheritedAddressSpace : 0x78 'x'
+0x001 ReadImageFileExecOptions : 0xff ''
+0x002 BeingDebugged : 0x97 ''
+0x003 BitField : 0 ''
+0x003 ImageUsesLargePages : 0y0
+0x003 IsProtectedProcess : 0y0
+0x003 IsLegacyProcess : 0y0
+0x003 IsImageDynamicallyRelocated : 0y0
+0x003 SkipPatchingUser32Forwarders : 0y0
+0x003 SpareBits : 0y000
+0x004 Mutant : 0x00980000 Void
+0x008 ImageBaseAddress : 0x0097f000 Void
+0x00c Ldr : (null)
+0x010 ProcessParameters : 0x00001e00 _RTL_USER_PROCESS_PARAMETERS
+0x014 SubSystemData : (null)
+0x018 ProcessHeap : 0x7ffdb000 Void
+0x01c FastPebLock : (null)
+0x020 AtlThunkSListPtr : 0x00000dcc Void
+0x024 IFEOKey : 0x00000ed4 Void
+0x028 CrossProcessFlags : 0
+0x028 ProcessInJob : 0y0
+0x028 ProcessInitializing : 0y0
+0x028 ProcessUsingVEH : 0y0
+0x028 ProcessUsingVCH : 0y0
+0x028 ProcessUsingFTH : 0y0
+0x028 ReservedBits0 : 0y000000000000000000000000000 (0)
+0x02c KernelCallbackTable : 0x7ffdb02c Void
+0x02c UserSharedInfoPtr : 0x7ffdb02c Void
+0x030 SystemReserved : [1] 0x7ffda000
+0x034 AtlThunkSListPtr32 : 0x57
+0x038 ApiSetMap : (null)
+0x03c TlsExpansionCounter : 0
+0x040 TlsBitmap : (null)
+0x044 TlsBitmapBits : [2] 0
+0x04c ReadOnlySharedMemoryBase : (null)
+0x050 HotpatchInformation : (null)
+0x054 ReadOnlyStaticServerData : (null)
+0x058 AnsiCodePageData : (null)
+0x05c OemCodePageData : (null)
+0x060 UnicodeCaseTableData : (null)
+0x064 NumberOfProcessors : 0
+0x068 NtGlobalFlag : 0
+0x070 CriticalSectionTimeout : _LARGE_INTEGER 0x0
+0x078 HeapSegmentReserve : 0
+0x07c HeapSegmentCommit : 0
+0x080 HeapDeCommitTotalFreeThreshold : 0
+0x084 HeapDeCommitFreeBlockThreshold : 0
+0x088 NumberOfHeaps : 0
+0x08c MaximumNumberOfHeaps : 0
+0x090 ProcessHeaps : (null)
+0x094 GdiSharedHandleTable : (null)
+0x098 ProcessStarterHelper : (null)
+0x09c GdiDCAttributeList : 0
+0x0a0 LoaderLock : (null)
+0x0a4 OSMajorVersion : 0
+0x0a8 OSMinorVersion : 0
+0x0ac OSBuildNumber : 0
+0x0ae OSCSDVersion : 0
+0x0b0 OSPlatformId : 0
+0x0b4 ImageSubsystem : 0
+0x0b8 ImageSubsystemMajorVersion : 0
+0x0bc ImageSubsystemMinorVersion : 0
+0x0c0 ActiveProcessAffinityMask : 0
+0x0c4 GdiHandleBuffer : [34] 0x804
+0x14c PostProcessInitRoutine : (null)
+0x150 TlsExpansionBitmap : (null)
+0x154 TlsExpansionBitmapBits : [32] 0
+0x1d4 SessionId : 0
+0x1d8 AppCompatFlags : _ULARGE_INTEGER 0x0
+0x1e0 AppCompatFlagsUser : _ULARGE_INTEGER 0x0
+0x1e8 pShimData : (null)
+0x1ec AppCompatInfo : (null)
+0x1f0 CSDVersion : _UNICODE_STRING ""
+0x1f8 ActivationContextData : (null)
+0x1fc ProcessAssemblyStorageMap : (null)
+0x200 SystemDefaultActivationContextData : (null)
+0x204 SystemAssemblyStorageMap : (null)
+0x208 MinimumStackCommit : 0
+0x20c FlsCallback : (null)
+0x210 FlsListHead : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x218 FlsBitmap : (null)
+0x21c FlsBitmapBits : [4] 0
+0x22c FlsHighIndex : 0
+0x230 WerRegistrationData : (null)
+0x234 WerShipAssertPtr : (null)
+0x238 pContextData : (null)
+0x23c pImageHeaderHash : (null)
+0x240 TracingFlags : 0
+0x240 HeapTracingEnabled : 0y0
+0x240 CritSecTracingEnabled : 0y0
+0x240 SpareTracingBits : 0y000000000000000000000000000000 (0)
kd> dt _RTL_USER_PROCESS_PARAMETERS 0x00001e00
csrss!_RTL_USER_PROCESS_PARAMETERS
+0x000 MaximumLength : ??
+0x004 Length : ??
+0x008 Flags : ??
+0x00c DebugFlags : ??
+0x010 ConsoleHandle : ????
+0x014 ConsoleFlags : ??
+0x018 StandardInput : ????
+0x01c StandardOutput : ????
+0x020 StandardError : ????
+0x024 CurrentDirectory : _CURDIR
+0x030 DllPath : _UNICODE_STRING
+0x038 ImagePathName : _UNICODE_STRING
+0x040 CommandLine : _UNICODE_STRING
+0x048 Environment : ????
+0x04c StartingX : ??
+0x050 StartingY : ??
+0x054 CountX : ??
+0x058 CountY : ??
+0x05c CountCharsX : ??
+0x060 CountCharsY : ??
+0x064 FillAttribute : ??
+0x068 WindowFlags : ??
+0x06c ShowWindowFlags : ??
+0x070 WindowTitle : _UNICODE_STRING
+0x078 DesktopInfo : _UNICODE_STRING
+0x080 ShellInfo : _UNICODE_STRING
+0x088 RuntimeData : _UNICODE_STRING
+0x090 CurrentDirectores : [32] _RTL_DRIVE_LETTER_CURDIR
+0x290 EnvironmentSize : ??
+0x294 EnvironmentVersion : ??
Memory read error 00002094
这样查看其他进程内存信息查看不到。全是??,
所以使用上述命令
kd> .process /p 876589b0
Implicit process is now 876589b0
.cache forcedecodeuser done
kd> dt _EPROCESS 876589b0
ntdll!_EPROCESS
+0x000 Pcb : _KPROCESS
+0x098 ProcessLock : _EX_PUSH_LOCK
+0x0a0 CreateTime : _LARGE_INTEGER 0x1d5108b`d0d0aa48
+0x0a8 ExitTime : _LARGE_INTEGER 0x0
+0x0b0 RundownProtect : _EX_RUNDOWN_REF
+0x0b4 UniqueProcessId : 0x0000056c Void
+0x0b8 ActiveProcessLinks : _LIST_ENTRY [ 0x8766bb08 - 0x87649cf8 ]
+0x0c0 ProcessQuotaUsage : [2] 0x664c
+0x0c8 ProcessQuotaPeak : [2] 0x7a5c
+0x0d0 CommitCharge : 0x1db3
+0x0d4 QuotaBlock : 0x874cc580 _EPROCESS_QUOTA_BLOCK
+0x0d8 CpuQuotaBlock : (null)
+0x0dc PeakVirtualSize : 0x104e5000
+0x0e0 VirtualSize : 0xe5de000
+0x0e4 SessionProcessLinks : _LIST_ENTRY [ 0x875f5114 - 0x87649d24 ]
+0x0ec DebugPort : (null)
+0x0f0 ExceptionPortData : 0x873f3828 Void
+0x0f0 ExceptionPortValue : 0x873f3828
+0x0f0 ExceptionPortState : 0y000
+0x0f4 ObjectTable : 0x8c838650 _HANDLE_TABLE
+0x0f8 Token : _EX_FAST_REF
+0x0fc WorkingSetPage : 0x1e387
+0x100 AddressCreationLock : _EX_PUSH_LOCK
+0x104 RotateInProgress : (null)
+0x108 ForkInProgress : (null)
+0x10c HardwareTrigger : 0
+0x110 PhysicalVadRoot : (null)
+0x114 CloneRoot : (null)
+0x118 NumberOfPrivatePages : 0xfd7
+0x11c NumberOfLockedPages : 0
+0x120 Win32Process : 0xfe962380 Void
+0x124 Job : (null)
+0x128 SectionObject : 0x8c838590 Void
+0x12c SectionBaseAddress : 0x00030000 Void
+0x130 Cookie : 0x417f32c2
+0x134 Spare8 : 0
+0x138 WorkingSetWatch : (null)
+0x13c Win32WindowStation : 0x00000030 Void
+0x140 InheritedFromUniqueProcessId : 0x0000054c Void
+0x144 LdtInformation : (null)
+0x148 VdmObjects : (null)
+0x14c ConsoleHostProcess : 0
+0x150 DeviceMap : 0x8e9d8a38 Void
+0x154 EtwDataSource : 0x877464c0 Void
+0x158 FreeTebHint : 0x7ffdd000 Void
+0x160 PageDirectoryPte : _HARDWARE_PTE_X86
+0x160 Filler : 0
+0x168 Session : 0x8ef75000 Void
+0x16c ImageFileName : [15] "explorer.exe"
+0x17b PriorityClass : 0x2 ''
+0x17c JobLinks : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x184 LockedPagesList : (null)
+0x188 ThreadListHead : _LIST_ENTRY [ 0x876588e8 - 0x8748b630 ]
+0x190 SecurityPort : (null)
+0x194 PaeTop : 0x867cc2c0 Void
+0x198 ActiveThreads : 0x1a
+0x19c ImagePathHash : 0x7a3328da
+0x1a0 DefaultHardErrorProcessing : 0
+0x1a4 LastThreadExitStatus : 0n0
+0x1a8 Peb : 0x7ffdb000 _PEB
+0x1ac PrefetchTrace : _EX_FAST_REF
+0x1b0 ReadOperationCount : _LARGE_INTEGER 0x745
+0x1b8 WriteOperationCount : _LARGE_INTEGER 0xb
+0x1c0 OtherOperationCount : _LARGE_INTEGER 0x24ce
+0x1c8 ReadTransferCount : _LARGE_INTEGER 0x1dc751
+0x1d0 WriteTransferCount : _LARGE_INTEGER 0x2a4
+0x1d8 OtherTransferCount : _LARGE_INTEGER 0x46d39
+0x1e0 CommitChargeLimit : 0
+0x1e4 CommitChargePeak : 0x2235
+0x1e8 AweInfo : (null)
+0x1ec SeAuditProcessCreationInfo : _SE_AUDIT_PROCESS_CREATION_INFO
+0x1f0 Vm : _MMSUPPORT
+0x25c MmProcessLinks : _LIST_ENTRY [ 0x8766bcac - 0x87649e9c ]
+0x264 HighestUserAddress : 0x7fff0000 Void
+0x268 ModifiedPageCount : 0x5d
+0x26c Flags2 : 0xd000
+0x26c JobNotReallyActive : 0y0
+0x26c AccountingFolded : 0y0
+0x26c NewProcessReported : 0y0
+0x26c ExitProcessReported : 0y0
+0x26c ReportCommitChanges : 0y0
+0x26c LastReportMemory : 0y0
+0x26c ReportPhysicalPageChanges : 0y0
+0x26c HandleTableRundown : 0y0
+0x26c NeedsHandleRundown : 0y0
+0x26c RefTraceEnabled : 0y0
+0x26c NumaAware : 0y0
+0x26c ProtectedProcess : 0y0
+0x26c DefaultPagePriority : 0y101
+0x26c PrimaryTokenFrozen : 0y1
+0x26c ProcessVerifierTarget : 0y0
+0x26c StackRandomizationDisabled : 0y0
+0x26c AffinityPermanent : 0y0
+0x26c AffinityUpdateEnable : 0y0
+0x26c PropagateNode : 0y0
+0x26c ExplicitAffinity : 0y0
+0x270 Flags : 0x144d0801
+0x270 CreateReported : 0y1
+0x270 NoDebugInherit : 0y0
+0x270 ProcessExiting : 0y0
+0x270 ProcessDelete : 0y0
+0x270 Wow64SplitPages : 0y0
+0x270 VmDeleted : 0y0
+0x270 OutswapEnabled : 0y0
+0x270 Outswapped : 0y0
+0x270 ForkFailed : 0y0
+0x270 Wow64VaSpace4Gb : 0y0
+0x270 AddressSpaceInitialized : 0y10
+0x270 SetTimerResolution : 0y0
+0x270 BreakOnTermination : 0y0
+0x270 DeprioritizeViews : 0y0
+0x270 WriteWatch : 0y0
+0x270 ProcessInSession : 0y1
+0x270 OverrideAddressSpace : 0y0
+0x270 HasAddressSpace : 0y1
+0x270 LaunchPrefetched : 0y1
+0x270 InjectInpageErrors : 0y0
+0x270 VmTopDown : 0y0
+0x270 ImageNotifyDone : 0y1
+0x270 PdeUpdateNeeded : 0y0
+0x270 VdmAllowed : 0y0
+0x270 CrossSessionCreate : 0y0
+0x270 ProcessInserted : 0y1
+0x270 DefaultIoPriority : 0y010
+0x270 ProcessSelfDelete : 0y0
+0x270 SetTimerResolutionLink : 0y0
+0x274 ExitStatus : 0n259
+0x278 VadRoot : _MM_AVL_TABLE
+0x298 AlpcContext : _ALPC_PROCESS_CONTEXT
+0x2a8 TimerResolutionLink : _LIST_ENTRY [ 0x0 - 0x0 ]
+0x2b0 RequestedTimerResolution : 0
+0x2b4 ActiveThreadsHighWatermark : 0x28
+0x2b8 SmallestTimerResolution : 0
+0x2bc TimerResolutionStackRecord : (null)
kd> dt _PEB 0x7ffdb000
csrss!_PEB
+0x000 InheritedAddressSpace : 0 ''
+0x001 ReadImageFileExecOptions : 0 ''
+0x002 BeingDebugged : 0 ''
+0x003 BitField : 0x8 ''
+0x003 ImageUsesLargePages : 0y0
+0x003 IsProtectedProcess : 0y0
+0x003 IsLegacyProcess : 0y0
+0x003 IsImageDynamicallyRelocated : 0y1
+0x003 SkipPatchingUser32Forwarders : 0y0
+0x003 SpareBits : 0y000
+0x004 Mutant : 0xffffffff Void
+0x008 ImageBaseAddress : 0x00030000 Void
+0x00c Ldr : 0x77047880 _PEB_LDR_DATA
+0x010 ProcessParameters : 0x003f1090 _RTL_USER_PROCESS_PARAMETERS
+0x014 SubSystemData : (null)
+0x018 ProcessHeap : 0x003f0000 Void
+0x01c FastPebLock : 0x77047380 _RTL_CRITICAL_SECTION
+0x020 AtlThunkSListPtr : (null)
+0x024 IFEOKey : (null)
+0x028 CrossProcessFlags : 0
+0x028 ProcessInJob : 0y0
+0x028 ProcessInitializing : 0y0
+0x028 ProcessUsingVEH : 0y0
+0x028 ProcessUsingVCH : 0y0
+0x028 ProcessUsingFTH : 0y0
+0x028 ReservedBits0 : 0y000000000000000000000000000 (0)
+0x02c KernelCallbackTable : 0x754dd568 Void
+0x02c UserSharedInfoPtr : 0x754dd568 Void
+0x030 SystemReserved : [1] 0
+0x034 AtlThunkSListPtr32 : 0x294e670
+0x038 ApiSetMap : 0x771b0000 Void
+0x03c TlsExpansionCounter : 0
+0x040 TlsBitmap : 0x77047260 Void
+0x044 TlsBitmapBits : [2] 0xffffffff
+0x04c ReadOnlySharedMemoryBase : 0x7f6f0000 Void
+0x050 HotpatchInformation : (null)
+0x054 ReadOnlyStaticServerData : 0x7f6f0590 -> (null)
+0x058 AnsiCodePageData : 0x7ffa0000 Void
+0x05c OemCodePageData : 0x7ffa0000 Void
+0x060 UnicodeCaseTableData : 0x7ffd0024 Void
+0x064 NumberOfProcessors : 1
+0x068 NtGlobalFlag : 0
+0x070 CriticalSectionTimeout : _LARGE_INTEGER 0xffffe86d`079b8000
+0x078 HeapSegmentReserve : 0x100000
+0x07c HeapSegmentCommit : 0x2000
+0x080 HeapDeCommitTotalFreeThreshold : 0x10000
+0x084 HeapDeCommitFreeBlockThreshold : 0x1000
+0x088 NumberOfHeaps : 0x11
+0x08c MaximumNumberOfHeaps : 0x20
+0x090 ProcessHeaps : 0x07189480 -> 0x003f0000 Void
+0x094 GdiSharedHandleTable : 0x005c0000 Void
+0x098 ProcessStarterHelper : (null)
+0x09c GdiDCAttributeList : 0x14
+0x0a0 LoaderLock : 0x77047340 _RTL_CRITICAL_SECTION
+0x0a4 OSMajorVersion : 6
+0x0a8 OSMinorVersion : 1
+0x0ac OSBuildNumber : 0x1db1
+0x0ae OSCSDVersion : 0x100
+0x0b0 OSPlatformId : 2
+0x0b4 ImageSubsystem : 2
+0x0b8 ImageSubsystemMajorVersion : 6
+0x0bc ImageSubsystemMinorVersion : 1
+0x0c0 ActiveProcessAffinityMask : 1
+0x0c4 GdiHandleBuffer : [34] 0
+0x14c PostProcessInitRoutine : (null)
+0x150 TlsExpansionBitmap : 0x77047268 Void
+0x154 TlsExpansionBitmapBits : [32] 0x3f
+0x1d4 SessionId : 1
+0x1d8 AppCompatFlags : _ULARGE_INTEGER 0x0
+0x1e0 AppCompatFlagsUser : _ULARGE_INTEGER 0x0
+0x1e8 pShimData : (null)
+0x1ec AppCompatInfo : (null)
+0x1f0 CSDVersion : _UNICODE_STRING "Service Pack 1"
+0x1f8 ActivationContextData : 0x00310000 _ACTIVATION_CONTEXT_DATA
+0x1fc ProcessAssemblyStorageMap : 0x004238a0 _ASSEMBLY_STORAGE_MAP
+0x200 SystemDefaultActivationContextData : 0x00300000 _ACTIVATION_CONTEXT_DATA
+0x204 SystemAssemblyStorageMap : 0x00400fe8 _ASSEMBLY_STORAGE_MAP
+0x208 MinimumStackCommit : 0
+0x20c FlsCallback : 0x00402a30 _FLS_CALLBACK_INFO
+0x210 FlsListHead : _LIST_ENTRY [ 0x402718 - 0x719fb00 ]
+0x218 FlsBitmap : 0x77047270 Void
+0x21c FlsBitmapBits : [4] 0x1f
+0x22c FlsHighIndex : 4
+0x230 WerRegistrationData : 0x01f40000 Void
+0x234 WerShipAssertPtr : (null)
+0x238 pContextData : 0x00320000 Void
+0x23c pImageHeaderHash : (null)
+0x240 TracingFlags : 0
+0x240 HeapTracingEnabled : 0y0
+0x240 CritSecTracingEnabled : 0y0
+0x240 SpareTracingBits : 0y000000000000000000000000000000 (0)
kd> dt _RTL_USER_PROCESS_PARAMETERS 0x003f1090
csrss!_RTL_USER_PROCESS_PARAMETERS
+0x000 MaximumLength : 0x6c4
+0x004 Length : 0x6c4
+0x008 Flags : 0x6001
+0x00c DebugFlags : 0
+0x010 ConsoleHandle : (null)
+0x014 ConsoleFlags : 0
+0x018 StandardInput : (null)
+0x01c StandardOutput : (null)
+0x020 StandardError : (null)
+0x024 CurrentDirectory : _CURDIR
+0x030 DllPath : _UNICODE_STRING "C:Windows;C:Windowssystem32;C:Windowssystem;C:Windows;.;C:Windowssystem32;C:Windows;C:WindowsSystem32Wbem;C:WindowsSystem32WindowsPowerShellv1.0"
+0x038 ImagePathName : _UNICODE_STRING "C:WindowsExplorer.EXE"
+0x040 CommandLine : _UNICODE_STRING "C:WindowsExplorer.EXE"
+0x048 Environment : 0x004db748 Void
+0x04c StartingX : 0
+0x050 StartingY : 0
+0x054 CountX : 0
+0x058 CountY : 0
+0x05c CountCharsX : 0
+0x060 CountCharsY : 0x804
+0x064 FillAttribute : 0x300000
+0x068 WindowFlags : 1
+0x06c ShowWindowFlags : 1
+0x070 WindowTitle : _UNICODE_STRING "C:WindowsExplorer.EXE"
+0x078 DesktopInfo : _UNICODE_STRING "Winsta0Default"
+0x080 ShellInfo : _UNICODE_STRING "C:WindowsExplorer.EXE"
+0x088 RuntimeData : _UNICODE_STRING ""
+0x090 CurrentDirectores : [32] _RTL_DRIVE_LETTER_CURDIR
+0x290 EnvironmentSize : 0x8a6
+0x294 EnvironmentVersion : 7
就可以查看到值了。
线程类似。
x86查看SSDT表与SHDOWSSDT
最后
以上就是如意金鱼最近收集整理的关于Windbg使用笔记断点显示内存修改内存栈查看命令进程线程命令x86查看SSDT表与SHDOWSSDT的全部内容,更多相关Windbg使用笔记断点显示内存修改内存栈查看命令进程线程命令x86查看SSDT表与SHDOWSSDT内容请搜索靠谱客的其他文章。





发表评论 取消回复